Opinion stories - Page 101

What the wide-area network (WAN) management of the future looks like
Thu, 16th Jul 2020
#
network infrastructure
#
sd-wan
#
sdn
Organisations need to future-proof their WAN to improve network performance and address security vulnerabilities.

Closing the cloud skills gap: How certification can maximise cloud investments & keep staff happy
Fri, 10th Jul 2020
#
edutech
#
education, learning & training
#
opinion
Critical skills shortage in cloud computing hindering business development and digital transformation, warns report. #CloudSkills #TechIndustry.
Why enabling a remote workforce requires converging security at the edge
Tue, 7th Jul 2020
#
iaas
#
casb
#
dlp
CASB and SASE solutions are crucial for protecting enterprise data from both insider and outsider threats, says report.

The 5 most common multi-factor authentication (MFA) methods
Tue, 7th Jul 2020
#
mfa
#
cloud security
#
iam
Multi-factor authentication isn't flawless; discover the 5 most prevalent methods, their issues, and the delicate balance between security and usability.
How print services can improve productivity
Fri, 3rd Jul 2020
#
printing
#
cloud printing
#
opinion
Printing remains an essential element of business operations - whether employees are present in the office, working from home, or travelling between offices.

Enhancing the customer experience with data
Mon, 29th Jun 2020
#
crm
#
data analytics
#
cx
Customers don't have the time or patience for companies to figure it out; they go where they have the easiest, most satisfying experience.

The need for speed: What if tech could work as fast as your imagination?
Thu, 25th Jun 2020
#
crm
#
data analytics
#
cx
COVID-19 has forced businesses to adapt quickly and embrace disruption. Speed is now crucial in this rapidly changing market. #business #COVID19.

How to keep true, accurate records for legal compliance
Tue, 23rd Jun 2020
#
document management
#
ecm
#
martech
Failing to capture true and accurate records can lead to companies being in breach of the law, as well as the risk of breaching contracts with clients.

In IT security, 'good enough' is no longer good enough
Thu, 18th Jun 2020
#
malware
#
phishing
#
email security
Cyber attackers live by the motto 'Never let a good crisis go to waste', and COVID-19 delivers a perfect storm of opportunity for them.

Security spotlight on recent breaches highlights need for effective CASBs
Fri, 12th Jun 2020
#
iaas
#
casb
#
dlp
Recent major data breaches affecting millions highlight the urgent need for effective CASBs to safeguard against threats, especially in BYOD environments.

A security by design approach for cybersecurity
Tue, 9th Jun 2020
#
advanced persistent threat protection
#
risk & compliance
#
cybersecurity
Your website faces attacks from nefarious elements with financial gain and industrial sabotage high on their list of motivations.

New data center network architecture offers latency and throughput
Mon, 8th Jun 2020
#
network infrastructure
#
cloud services
#
network management
During a data center refresh cycle only an end node transceiver upgrade would be necessary, leading to greater cost savings.

All we need to know about reverse proxy
Thu, 4th Jun 2020
#
iaas
#
casb
#
byod
Understanding reverse proxies is essential for modern organisations seeking robust cloud security. Discover why this architecture stands out.

A winning proposition for critical infrastructure
Thu, 28th May 2020
#
firewalls
#
network infrastructure
#
surveillance
Network surveillance not only secures critical infrastructure but also boosts operational efficiency and health and safety practices, proving to be invaluable.

Chinks in the armour: Why the post COVID-19 cloud is easy game for cybercriminals
Thu, 28th May 2020
#
devops
#
apm
#
cybersecurity
Now's the time for CIOs to pause and make sure their digital transformation projects are fit for today, and the future.

Five wine-tasting tips that should be applied to network security
Mon, 25th May 2020
#
firewalls
#
network infrastructure
#
data analytics
Applying wine-tasting strategies to network security offers novel insights. Discover five tips to better identify network vulnerabilities and threats.

How DDoS protection is like a car's airbags
Mon, 18th May 2020
#
ddos
#
cybersecurity
#
opinion
DDoS attacks may occur infrequently, but the damages are severe. Why organisations still need dedicated DDoS protection. #cybersecurity #DDoS.

To work like a disrupter, change the way you work with data and analytics
Fri, 15th May 2020
#
data analytics
#
martech
#
planning
What do companies like Netflix, Airbnb, Spotify and Lyft know that you don't know? What do these companies have that you might be lacking?.
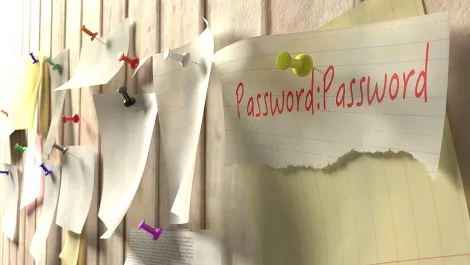
Six practical tips for better password practice
Wed, 6th May 2020
#
mfa
#
iam
#
cybersecurity
UK's National Cyber Security Centre reveals the most hacked passwords of 2019, including '123456' and 'password'.

AI is powering a shift in digital customer engagement
Wed, 6th May 2020
#
crm
#
uc
#
martech
AI-driven digital employees are revolutionising customer engagement as companies adapt to post-pandemic demands, cutting costs and boosting satisfaction.